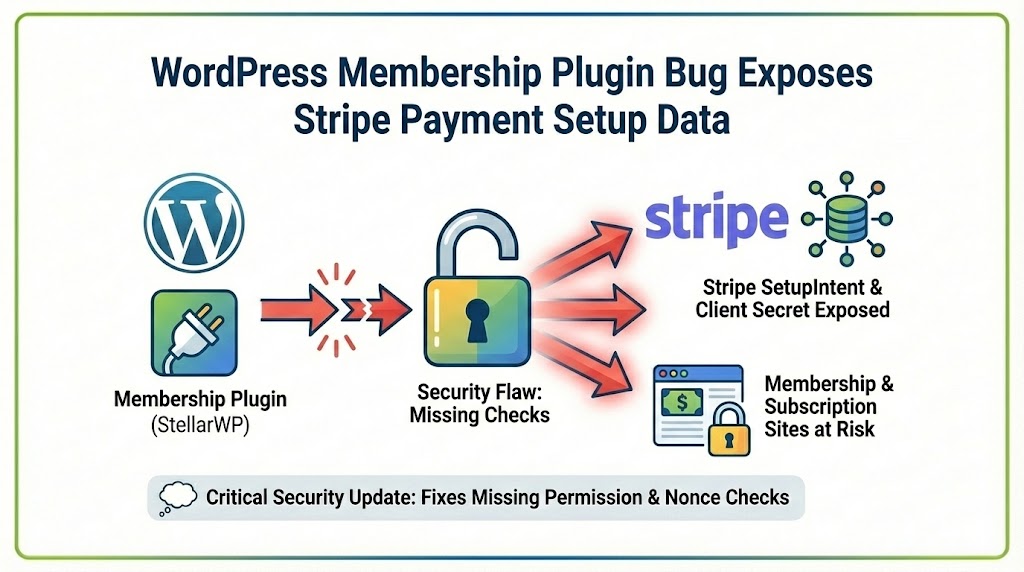
A newly disclosed security flaw in a popular WordPress membership plugin could expose sensitive Stripe payment setup information, putting thousands of membership and subscription sites at risk.
The vulnerability affects Membership Plugin – Restrict Content by StellarWP and allows unauthenticated attackers to access Stripe SetupIntent data, including client secrets that should never be publicly exposed. Security researchers have rated the issue high severity (CVSS 8.2).
Why This Vulnerability Is Serious
Unlike many WordPress security issues that require a compromised user account, this flaw can be exploited without logging in. That significantly raises the risk profile, particularly for sites handling paid memberships or recurring billing.
Because the exposed data is tied to Stripe’s payment setup process, the issue has implications beyond content access—it touches financial infrastructure.
What Went Wrong Behind the Scenes
The vulnerability stems from missing security checks in how the plugin handles Stripe SetupIntents.
A Stripe SetupIntent is used to securely collect and store a customer’s payment method for future charges. Each SetupIntent includes a client_secret, which Stripe explicitly states must only be shared with the intended customer during a secure checkout flow.
In this case, the plugin failed to properly protect an internal function responsible for creating SetupIntents. As a result:
-
No authentication was required to trigger the endpoint
-
No capability or permission checks were enforced
-
User-controlled input was not adequately validated
This combination made it possible for attackers to retrieve Stripe SetupIntent client_secret values tied to memberships.
Why Exposing a Stripe client_secret Matters
Stripe’s documentation is explicit: client_secret values should never be stored, logged, or exposed beyond the intended user.
If leaked, these values can be misused to interact with Stripe’s payment APIs in unintended ways, potentially enabling unauthorized payment method setup or abuse of billing workflows.
While the flaw does not directly allow attackers to charge cards, it exposes sensitive payment setup data that should remain strictly private.
Scope of Impact
The issue affects all versions of the plugin up to and including 3.2.16. The plugin is used by up to 10,000 WordPress sites, many of which rely on it for managing paid memberships, subscriptions, and gated content.
Because the exploit does not depend on user roles or credentials, any vulnerable site is exposed as long as the plugin remains unpatched.
How the Issue Was Fixed
The vulnerability has been addressed in version 3.2.17 of the plugin.
According to the official changelog, the update includes:
-
Added nonce checks to prevent unauthorized requests
-
Added permission checks to Stripe payment-related functions
-
Improved input validation around payment setup workflows
These changes close the gaps that allowed unauthenticated access to Stripe SetupIntent data.
What Site Owners Should Do Immediately
If you are using Membership Plugin – Restrict Content by StellarWP:
-
Update to version 3.2.17 or newer immediately
-
Review Stripe activity logs for unexpected behavior
-
Rotate Stripe API keys if you suspect exposure
-
Audit any plugins that handle payments or tokens
Sites that process recurring payments or store payment methods should treat this update as urgent.
The Broader Security Takeaway
As WordPress plugins increasingly integrate with third-party payment platforms, token handling and access control become critical security boundaries.
This incident highlights a recurring risk: even without traditional exploits like code execution, exposing sensitive API credentials can create real financial and compliance consequences.
For site owners and agencies, regular plugin updates, security monitoring, and principle-of-least-privilege access remain essential—especially for plugins that touch payments.