 As many business owners and webmasters are all aware, spam leads via form mail are a regular issue in the web world. Spammers adopt a variety of novel techniques to achieve their desired aim. But spammers cannot be given a free ride either, and we need to devise adequate strategies to counter their unethical practices. This post is specifically aimed to highlight the methods generally adopted by spammers, and the appropriate strategies to counter them. Why am I posting about it? Because I deal with them all the time!
As many business owners and webmasters are all aware, spam leads via form mail are a regular issue in the web world. Spammers adopt a variety of novel techniques to achieve their desired aim. But spammers cannot be given a free ride either, and we need to devise adequate strategies to counter their unethical practices. This post is specifically aimed to highlight the methods generally adopted by spammers, and the appropriate strategies to counter them. Why am I posting about it? Because I deal with them all the time!
Methods Spammers Use to Hijack a Form
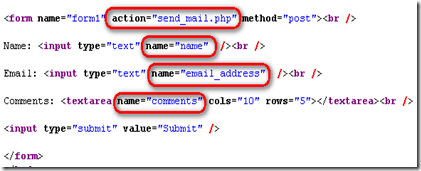
1. View-Source & URL submission
From the view source of web pages spammers know the field names as well as form action. Mostly this action page is used to send emails. For example, let's say the action is set to send_mail.php and the field names are name and email_address. Spammers can easily submit the values through a URL like www.yoursite.com/send_mail.php?name=Jeff&email_address=jeff@gmail.com. They will have an automated program to change the name and email and will keep on submitting the URL and mails are sent.
2. Page submission
In this case spammers use their own page to submit the form, and the form action is set to www.yoursite.com/mail.php. This method is used so that the POST validation used in the mail script is over ridden. This process can also be automated.
3. Manual submission
Here - spammers manually insert the values and submit the form. This method, however, is rarely used and the solution to block manual submission are limited.
Methods to Block Spam Leads
1. Captcha Code
Captcha code is one of the best methods used by web masters to avoid spam mail. It is dynamic text, and is generally shown in an image box. With every load / refresh click, the captcha code changes. The user will need to enter the text shown in the image to an adjacent text field. Successful submission can only be made when both the values match in the server side. Captcha code can be integrated easily using PHP Captcha Library. A simple captcha code using icons would be more preferable so as to make it more user- friendly.
2. Server side validation
Make sure that all mandatory fields are validated properly In the server side. PHP Filter function can be used to attain this. Java script validation won’t work if it’s disabled from the client browser; so server side validation is a must.
3. Filter all the Contents
Filter all the inputs from the form as spammers usually insert script tags or URLs in to form. It's then mandatory to strip the html tags and characters which are mostly used by spammers such as 'http://','mailto:','viagra' etc.
4. Use “POST” Method
Always make the form method to POST (<form method="post">) and the mail sending script should check only for POST values and not GET or REQUEST method. This will make sure that URL submission won't execute the script.
5. HTTP Referrer
HTTP Referer will make sure that the request has come from the same domain. Submission of forms from another domain can be blocked using this method.
6. Blocking IP
If spamming is done through manual submission, the solution is to block the IP address and for this the htaccess file can be used to implement this.
7. SQL Injection
If the form details are saved in to database use mysql_real_escape_string to avoid SQL injection.
Spam Mail Summary
All methods mentioned above, either singly or in combination, could insulate you from a host of spam leads that one is confronted with in every day life. These could ultimately turn out to be your bulwark against all unethical practices resorted to by spammers, who as we all know, do create inconveniences for all web masters.
This post, showcasing the methods adopted by spammers and the counter measured to be initiated, is intended to enlighten every one on the ways and means of making your website more secure and trustworthy. If none of these work, maybe you know where to buy a shot gun? :)




on
Great site. Lots of useful information here. I’m sending it to some pals ans additionally sharing in delicious. And of course, thanks in your effort!
on
Hi Bettann,
Glad you found our website informative.
Thanks for passing our site to your pals!
on
I've been trying to figure out how to get rid of all the stupid spam emails I get for a while now. I'm not the best with code but I'm going to give it a shot. Thanks for the write-up.
on
Hello,
Interesting post – thanks for the info. Curious about block IP addresses once an attempt has been made by the same IP address X amount of times. Any ideas on where I can find coding for this? Is this also something that can be done in the htaccess file?
Thanks again for the informative post!
on
Great tips. I have been using most of them to minimize the amount of spam. My htaccess file has bout 300 IP's that are blocked.
on
I have used captcha when developing ASP.NET websites. I have also used server side and client side validation to avoid spams. To be honest spammers always find a way to come up with something new to break the rules.
What really annoys me is email spam. My email address gets junk email everyday I can't believe.
By the way great post specially if you are PHP developer.
Thanks
Much appreciated.
on
Good information. Fortunately my sites haven't hit the spammers radar. I think I favor the captcha method as it looks the easiest by using a plugin.
on
This is a really good post, helped me learn how to block spammers from my web sites.
on
A very useful and informative one as it enlightens you on the ways and means of guarding yourself against the onslaught of these so called spammers. The tactics employed by these spammers are novel, and your advise to guard against them through appropriate tactics needs to be given due thought. A great post obviously
on
That was an informative post. Really nice article 🙂
Great step by step instructions.
Spam form mails are surely a major concern for every internet marketer as it engulfs all his efforts and measurements. These tips are sure to help in the fight against spam leads!